Let’s face it—Patch Management might not be the flashiest part of IT Asset Management, but it’s absolutely essential. A single missed update can be the open door hackers use to waltz into your systems. But by following a comprehensive set of Patch Management best practices, you can transform this daunting task into a smooth, efficient process that safeguards your organization like an invisible shield.
Here’s the kicker: according to a 2023 study by the Ponemon Institute, 44% of organizations lack a cohesive patch deployment strategy and instead rely on ad hoc schedules (or even emergency patch procedures). The report, titled The State of Patch Management in the Digital Workplace, highlights just how critical it is to prioritize patching processes and tools.
In this article, we’ll explore Patch Management best practices that every organization—big or small—can benefit from. We’re talking actionable tips to keep your systems secure, your operations smooth, and your IT team a lot less stressed. Let’s dive in!
Patch Management: a quick introduction
Let’s not get bogged down with the nitty-gritty details—here’s the gist. Patch Management is the process of acquiring, testing, and installing patches (a.k.a. software updates) to keep your systems up-to-date and secure. These patches fix bugs, close security gaps, and sometimes even throw in cool new features.
Why bother? Because it’s the cornerstone of strong cybersecurity. A solid Patch Management process ensures you:
- Fix flaws or bugs to prevent cyberattacks and costly data breaches.
- Comply with regulatory demands and avoid compliance headaches.
- Keep software running smoothly, because nobody wants apps or systems crashing unexpectedly.
- Enjoy the latest features that keep your organization ahead of the curve.
In short, Patch Management keeps your IT environment secure, stable, and ready for whatever comes next. Let’s move on to how you can get it right.
7 Patch Management best practices
Let’s be clear—Patch Management isn’t something you want to leave to chance. A well-structured patching process is your first line of defense against security vulnerabilities, data breaches, and software bugs. It’s how you keep your IT environment secure, compliant, and running smoothly. By following a thorough and organized Patch Management process, you ensure that operating systems and applications remain updated, reliable, and protected against cyberattacks.
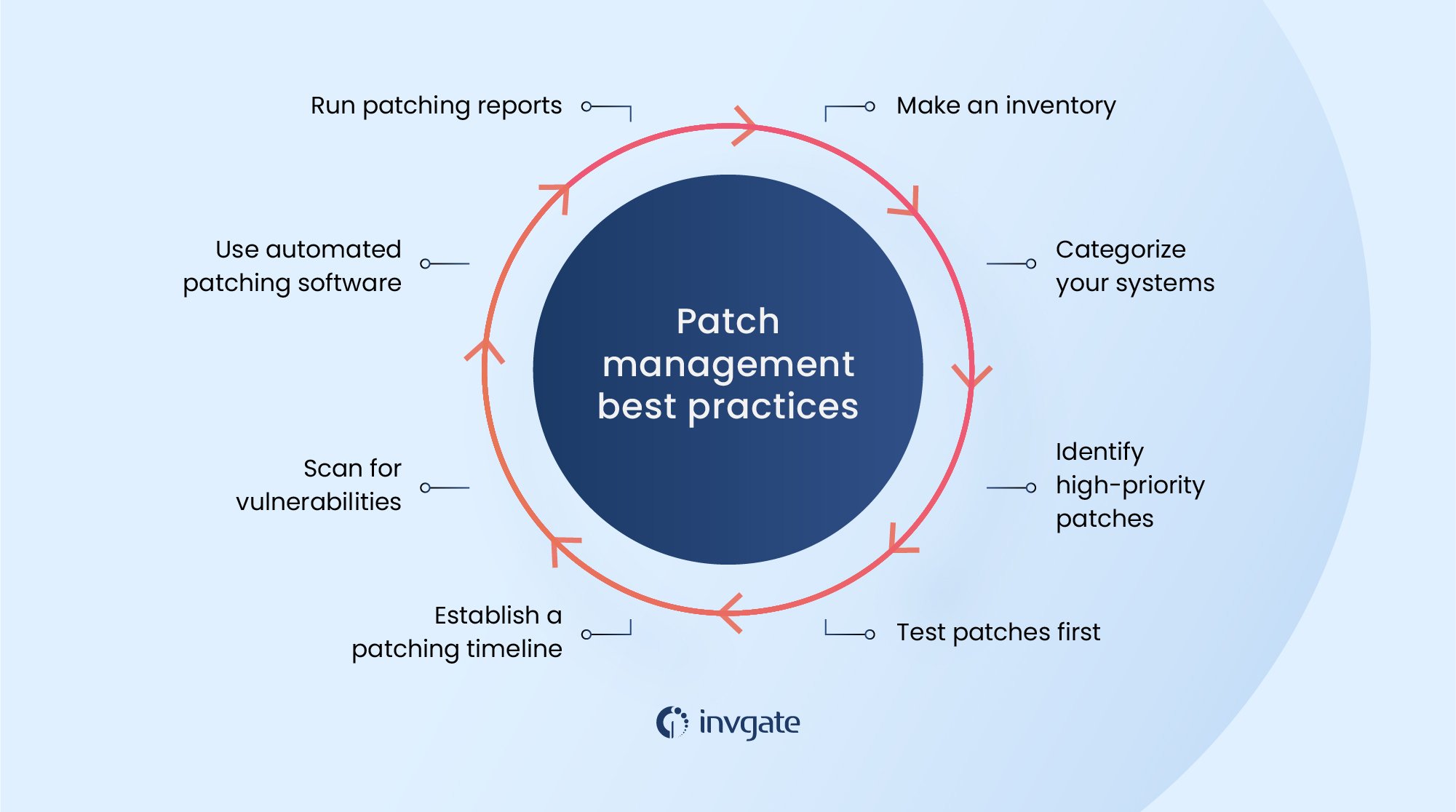
Sound good? Here’s a sneak peek at the 7 Patch Management best practices we’ll cover in detail:
- Take inventory of all devices, services, and dependencies in your IT infrastructure.
- Act with diligence to test, back up, and deploy patches promptly.
- Prioritize systems by categorizing assets and assigning risk levels.
- Test patches in a dedicated environment before rolling them out.
- Use automated Patch Management tools to streamline processes and reduce errors.
- Schedule auto-deployments to ensure regular updates without interruptions.
- Generate post-deployment reports to keep stakeholders informed and ensure compliance.
These practices aren’t just theoretical—they’re actionable steps to keep your organization secure and running like clockwork. Let’s break them down one by one.
#1. Make a thorough inventory
Start with a solid foundation: create a comprehensive inventory of assets within your IT infrastructure. This means documenting the names and versions of every software application in your network, including both native and third-party apps, operating systems, firewalls, antivirus programs, and other security tools installed across your devices.
Why is this crucial? Because you can’t protect or patch what you don’t know exists. By identifying every asset and dependency, you’ll have a clear picture of what needs updates and where vulnerabilities might lurk. This step is the cornerstone of a successful Patch Management process, ensuring that no device or software is left behind.
#2. Prioritize and act quickly with critical patches
When it comes to patching, diligence is non-negotiable. Once you’ve tested patches and created backups, it’s time to deploy. The urgency depends on how critical the update is and your Patch Management policies. High-priority updates—especially operating system patches—should take precedence. For example, delaying a critical Windows update can leave your systems vulnerable to attacks.
Take the WannaCry ransomware outbreak of 2017 as a cautionary tale. Microsoft had released a patch to address the vulnerability exploited by the malware, but only a fraction of users applied it. The result? A global cybersecurity disaster that could have been avoided with timely patching.
The lesson? Don’t delay. Stay proactive with updates, especially those addressing security vulnerabilities. Your speed today could mean avoiding major headaches tomorrow.
#3. Categorize systems and prioritize patches
Not all systems are created equal, and that’s why categorization is key. Start by conducting a thorough analysis to identify high-risk infrastructure or systems holding sensitive data. These should be prioritized for patch deployment to minimize vulnerabilities where they matter most.
Assigning risk levels to assets ensures you can focus on deploying the most critical patches first while safely delaying less urgent updates. This approach helps streamline your Patch Management process and makes the best use of available resources.
Using automated Patch Management tools can simplify this task by providing real-time insights into risk levels and patch prioritization. The right tools empower your IT team to act faster and smarter when applying patches.
#4. Test patches in a safe environment first
Before rolling out updates across your organization, always test patches in a dedicated test environment. This step ensures that patches work as intended and don’t cause unexpected issues, such as software conflicts or downtime.
Using a lab environment to simulate your production systems allows you to catch potential problems early and address them before they affect critical operations. By testing first, you minimize human error and ensure a smoother deployment when patches are applied in the production environment.
Testing might take extra time upfront, but it’s a worthwhile investment to avoid disruptions and ensure a successful patch deployment.
#5. Leverage automated Patch Management tools

Managing patches manually is a thing of the past. Patch automation streamlines the process, improves accuracy, and saves your IT team countless hours of manual effort. These tools are essential for handling complex environments with numerous devices and applications.
When choosing a solution, consider an IT Asset Management (ITAM) tool with robust Patch Management capabilities. Tools like InvGate Asset Management offer scalability, flexibility, and real-time monitoring, allowing you to track updates, visualize data, and deploy patches seamlessly.
Automation doesn’t just lighten the workload; it ensures no vulnerabilities slip through the cracks. From prioritizing critical patches to ensuring compliance, an automated approach is your key to efficient and effective Patch Management.
#6. Create a patch deployment schedule that fits your organization
Consistency is key to effective Patch Management, but there’s no one-size-fits-all schedule. The frequency of patch deployments should align with your organization’s size, resources, and risk level. Setting a clear timeline ensures regular updates while leaving room for proper testing and approvals.
For smaller organizations, a biweekly or weekly schedule might strike the right balance between maintaining security and minimizing disruption. Larger companies with complex IT environments may benefit from automated Patch Management tools that can handle more frequent updates, such as daily or twice-weekly deployments.
The goal is to establish a cadence that keeps your systems protected from both common vulnerabilities and more complex threats addressed by security patches. By tailoring your schedule to your organization’s needs, you’ll stay secure and compliant without overwhelming your IT team.
Monitor vendor patch announcements
Part of your schedule should include monitoring vendor patch announcements. These announcements provide critical updates about newly released patches and vulnerabilities, ensuring your organization acts promptly on high-priority updates.
#7. Document and report after deployment
The job isn’t done once the patches are deployed. Post-deployment reports are a key part of your Patch Management strategies, helping you refine processes and improve outcomes. These reports provide insights into what patches were applied, which systems were updated, and any vulnerabilities that remain.
Detailed documentation not only keeps management and auditors informed but also demonstrates compliance with industry standards and regulations. It’s an essential step to validate your organization’s security measures and to identify areas for improvement in future patching cycles.
A good Patch Management tool can automate this reporting, generating clear, actionable insights with minimal effort. This ensures that your team can focus on proactive security measures while maintaining a robust paper trail for audits.

Operating systems (OS) patching best practices
Operating systems are the backbone of your IT infrastructure, making their security and stability non-negotiable. While the Patch Management best practices we’ve discussed so far—like testing, prioritizing, and automating—apply to all systems, operating systems deserve special attention due to their foundational role. Neglecting OS patches can expose your organization to severe vulnerabilities, disrupt applications, and jeopardize compliance.
That said, the approach to patching varies between operating systems like Linux and Windows. Let’s explore the best practices for each.
Linux patching best practices
For Linux environments, automation is your best friend. Popular Linux Patch Management Tools like APT (for Ubuntu) or YUM/DNF (for Red Hat) can streamline the patching process by automatically fetching and applying updates. Regularly monitoring vendor patch announcements is essential to ensure you’re aware of critical security updates for your Linux distributions.
Another best practice is leveraging live patching tools, which allow you to apply kernel updates without requiring a reboot, minimizing downtime. Additionally, maintaining a dedicated test environment is crucial to prevent compatibility issues with custom applications or configurations.
Windows patching best practices
Windows environments often rely on centralized tools like Windows Server Update Services (WSUS) or Microsoft Endpoint Configuration Manager for managing patches across systems. These tools simplify deployment and ensure patches are prioritized based on criticality.
Testing is equally important here. Before applying updates organization-wide, use a lab environment to identify potential conflicts, especially for production-critical applications. Establishing a clear patching schedule and leveraging automated Patch Management tools ensures your Windows devices stay secure without disrupting day-to-day operations.
The bottom line
A thorough and well-organized patching process is crucial to ensure all software updates are applied promptly, whether immediately upon release or within a specific time frame outlined by your organization's Patch Management policy.
Implementing Patch Management best practices can make a significant difference. These include creating a comprehensive inventory of devices and services in your IT infrastructure, categorizing systems to prioritize critical updates, testing patches before deployment, and setting a patching schedule tailored to your organization's needs. Additionally, monitoring vendor patch announcements ensures you're always aware of new vulnerabilities and updates.
By following these practices and leveraging tools like InvGate Asset Management, your organization can enhance efficiency, strengthen its security posture, and stay ahead of potential threats.
Frequently Asked Questions
1. What is a Patch Management strategy?
A Patch Management strategy is a structured approach to handling software updates. It includes policies for prioritization, timelines for deployment, and processes for testing, automation, and reporting to ensure consistent and secure patching.
2. What is the ISO standard for Patch Management?
The ISO standard for Patch Management is ISO/IEC 27002:2022, which provides guidance on establishing controls for Vulnerability Management, including the deployment of patches to mitigate risks.
3. What are some common problems with Patch Management?
Common challenges include:
- Managing external devices like mobile phones or laptops, which may not follow standard patching procedures.
- Lack of visibility into deployed patches and vulnerable systems.
- Patch failures due to compatibility issues or incomplete deployments.
- Overreliance on manual processes, increasing the risk of errors.
Using automated Patch Management tools can address many of these issues.
4. What is the top challenge in implementing Patch Management?
The top challenge is managing external devices. If not monitored and patched properly, they can introduce vulnerabilities or malware into the organization's network, increasing cybersecurity risks.
5. How do Vulnerability Management and Patch Management best practices align?
Both practices focus on identifying, prioritizing, and mitigating risks. While Vulnerability Management involves identifying and assessing weaknesses, Patch Management resolves them by applying updates. Together, they create a proactive defense strategy.














